-
Completed
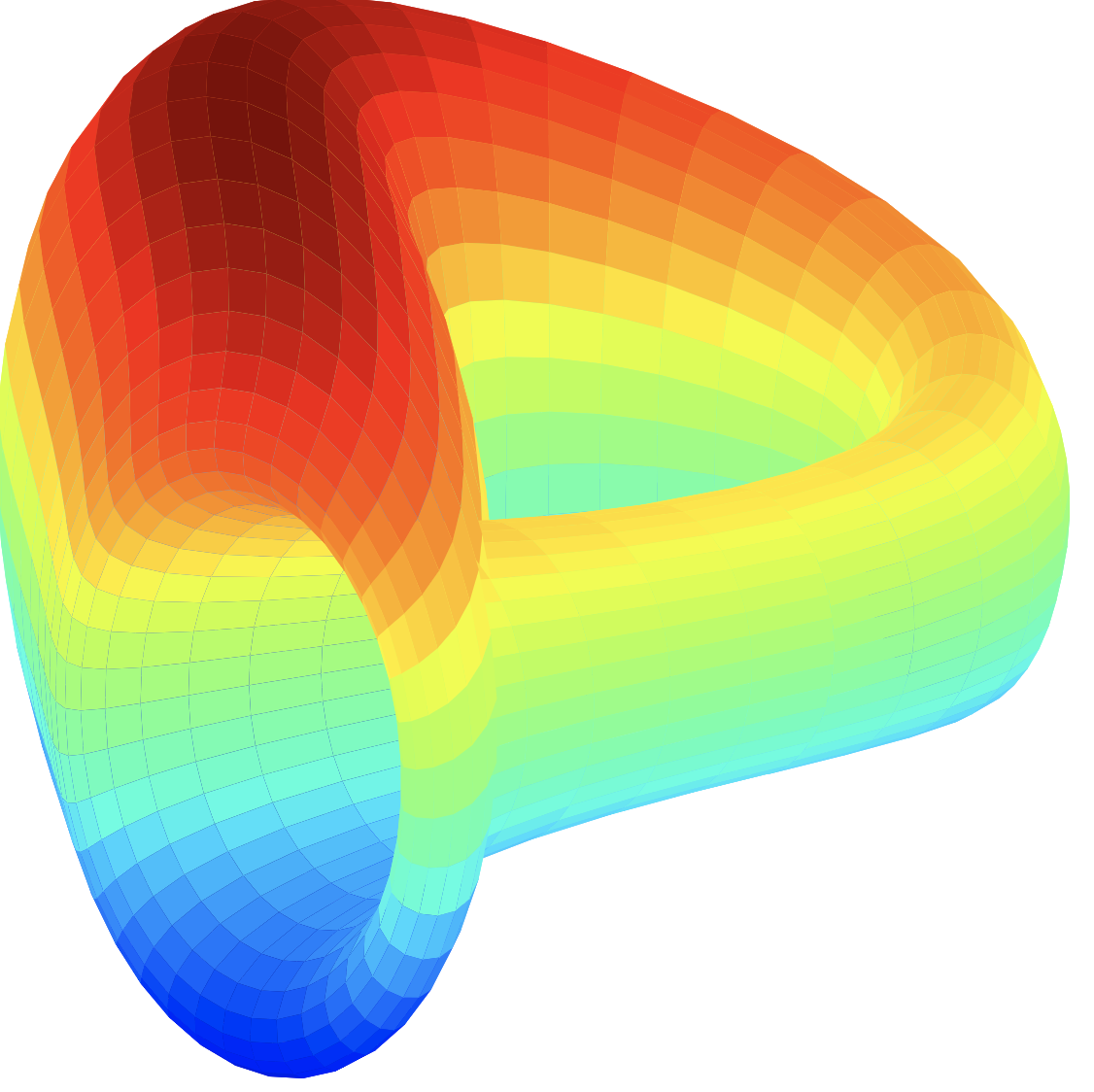
Clique V3 Campaign
As revealed in our 2023 roadmap article, STP is focused on its mission to build an ecosystem optimized for DAOs. We are progressing on our early initiative to build a platform of tools & infrastr
Max Award100
Start Date:
End Date:
-
Completed

Sonet x H.E.R DAO Bounty Event
Join Sonet x H.E.R DAO Blockzone Bounty Event and share a total of 6,500 MATIC
Max Award15 matic
Start Date:
End Date:
-
Completed
Clique DAO Reward Part II
Share $2,000 worth of STPT reward from Clique DAO Reward Part II
Max Award$5
Start Date:
End Date:
-
Completed
Clique DAO Reward
Share $2,000 worth of STPT reward in Clique DAO Reward
Max Award$5
Start Date:
End Date:
-
Completed

DeFine
Share 3,300 USDT rewards in DeFine Airdrop
Max Award$5
Start Date:
End Date:
-
Completed

Sumer.Money
Share a total of 5,000 USDT rewards
Max Award5
Start Date:
End Date:
-
Completed

Soda
Share 4,000 USDT rewards
Max Award5
Start Date:
End Date:
-
Completed

DAD
Participate in DAD airdrop and share 4000 USDT reward
Max Award$5
Start Date:
End Date:
-
Completed
RAI Finance
Participate in the RAI Finance airdrop and share 8,000 USDT token rewards
Max Award$65
Start Date:
End Date:
-
Completed

Deesse
Participate in the airdrop and share $5,000 USDT rewards!
Max Award$5
Start Date:
End Date:
-
Completed

PredictX
Participate in the PredictX airdrop and share $5,000 USDT rewards!
Max Award$5
Start Date:
End Date:
-
Completed

Talken
Participate in the Talken airdrop and share $9,000 airdrop rewards.
Max Award$3
Start Date:
End Date:
-
Completed

DeFine
Participate in the DeFine airdrop and share $5,000 airdrop rewards.
Max Award$10
Start Date:
End Date:
-
Completed

BigBang Core
Participate in the BigBang Core airdrop and share $10,000 worth of BBC token awards!
Max Award$5
Start Date:
End Date:
-
Completed

Lattice
Complete micro tasks for Lattice and share $10,000 worth of the Lattice token prize pool!
Max Award$6
Start Date:
End Date:
-
Completed

Akoin
Participate in the Akoin Airdrop and share $25,000 worth of awards
Max Award$10
Start Date:
End Date:
-
Completed

Klaytn
Participate in the Klaytn Airdrop and share $10,000 worth of KLAY token awards
Max Award$2
Start Date:
End Date:
-
Completed

Chromia
Complete micro tasks for Chromia and win $5,000 CHR token awards!
Max Award$11
Start Date:
End Date:
-
Completed

APM Coin
Participate in the Airdrop to win free APM Token!
Max Award$20
Start Date:
End Date: